PCB Importers: Import Wizard

Table of Contents
One task that has always proven difficult is moving electronic product designs from one design environment to another. Whether you’ve changed design tools or acquired designs from another company, there are a number of challenges involved in moving a project from one software platform to another, while maintaining design consistency. It’s a difficult and time-consuming process, but it has to be done.
INTRODUCTION
If a PCB designer has a design in one particular design tool format or program, such as Designspark PCB or Kicad PCB, and wants to use a different tool moving forward. What do they do? Do they re-enter the design from scratch into the new tool? This is costly and time-consuming, and will more than likely lead to discrepancies in layout between the two designs.
Instead, a PCB design import wizard is much more effective at importing the design directly from the old design tool into the new one. This saves time and minimizes chances of introducing unexpected design inconsistencies. Therefore, it’s essential that your design tools have import capabilities that are easy to use and support a wide range of design schematic and PCB layout formats, to accommodate designs imported from other PCB Design tools.
HURDLES WHEN CHANGING PCB DESIGN TOOLS
As Electronic Design Automation (EDA) tools become more and more widespread, several companies have introduced their own PCB design software into the market--with both advantages and disadvantages. However, one issue that has always been difficult to overcome is the transference of a PCB layout schematic capture between the different software platforms, while maintaining consistency.
There could be any number of reasons why a user would need to transfer a design from one platform to another. There could be budgetary reasons. Perhaps an executive decision was made to switch to a new EDA tool. Maybe you received some design projects from another company that uses different software. Or maybe you just need to pull up some old designs from a legacy version of your existing software, which has since been discontinued. Let’s take a look at a couple of these scenarios, and their repercussions.
The main reason a PCB designer would need to switch designs from one tool to another is because the company or organization they work for has made the business decision to change design tools, while the designer is in the middle of a project. When this happens, users then face not only the challenge of having to learn a new design tool, but the arduous task of replicating all of their designs from the old software, into the new software. This is procedure is time-consuming and introduces the possibility of inconsistency in the design. In particular, inexperience with the new software environment can lead to schematic symbols being redrawn incorrectly. This can in turn lead to errors in a previously-functioning design.
Similar issues can also arise when a designer works on a project that originated in another company. Say a former customer of one of your competitors was unhappy with the work they did, and now wants your team to complete it. They give you the schematics, but they were created in a different design tool. The document file is difficult even to open, much less edit. If you’re not careful, this could end up delaying the project and costing a lot of extra money.
You can even face challenges when using your own designs and your own software. The life cycle of a PCB project can last through several generations software versions. You go to update an old project, and find that the tool that was used to create the original design has become a legacy tool, if not completely obsolete. How do you make the changes in the current system without ending up with a lot of new errors and discrepancies that need to be corrected?
There are plenty of reasons why a designer would need to transfer a Printed Circuit Board schematic capture from one software platform to another. And each of these reasons comes with its own potential problems and compatibility issues, which can lead to design inconsistencies, costing both time and money. Fortunately, there’s a solution: Altium Designer assists designers in preventing these problems, allowing the user to import design schematics and PCB layouts quickly and easily from other sources without the usual errors and discrepancies. This is accomplished through the Altium Import Wizard.
IMPORT WIZARD FOR PCB SCHEMATICS
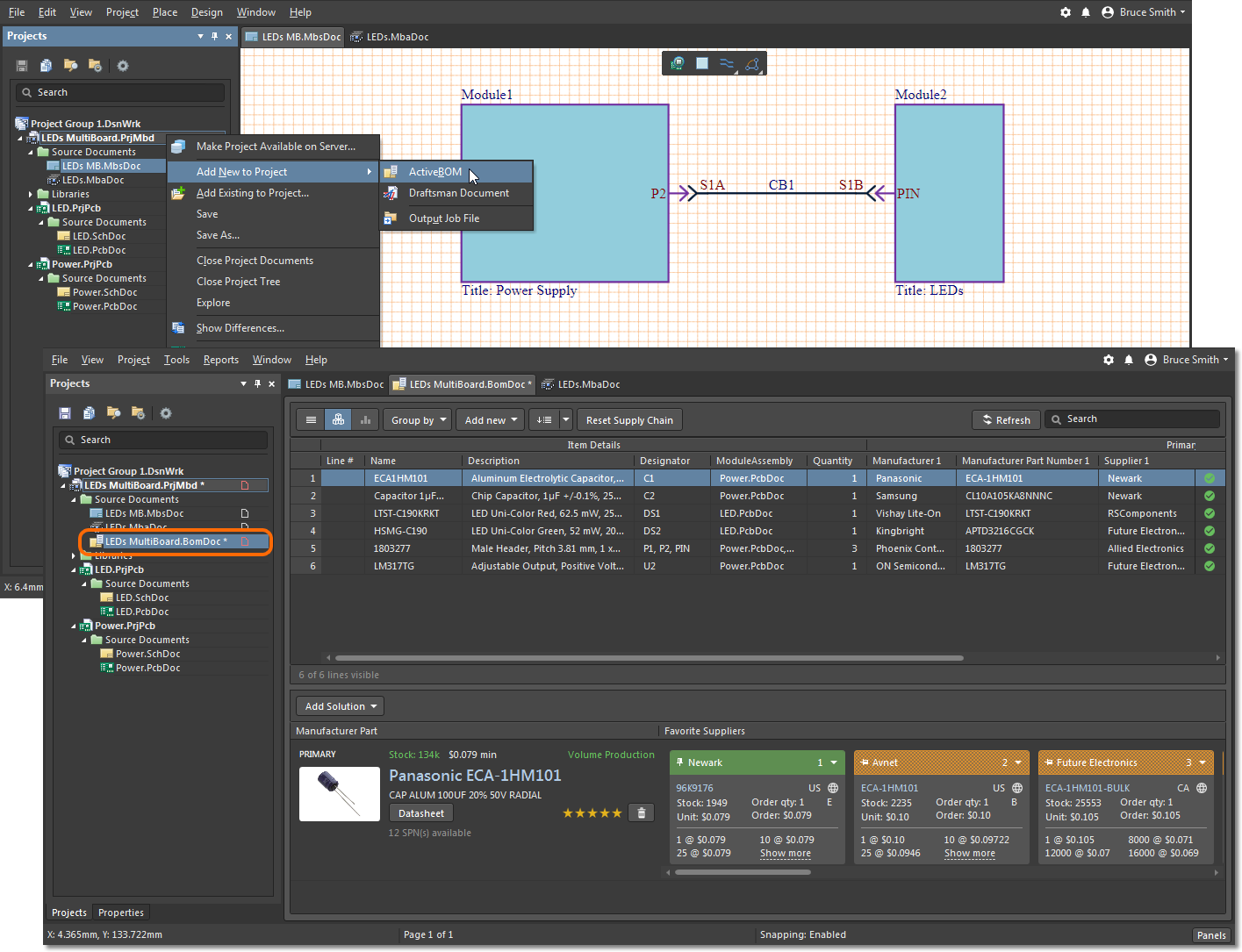
The Import Wizard unifies the importing process, allowing PCB designers to bring in a PCB layout from a variety of different PCB design tools. It walks you through the import process, handling both the Schematic and Printed Circuit Board PCB parts of the project, and managing the relationship between them. The architecture of the Import Wizard is designed to allow the easy addition of new importers, without adding complexity for the designer using the system. The importers are available through an easy installation window. Upon enabling it, a user can easily open the Import Wizard and view their available options.

Figure 1 - Import Wizard
The Import Wizard removes many of the headaches normally present in design translation, by analyzing your files and offering a variety of defaults and suggested settings for project structure, layer mapping, PCB footprint naming, and more. Complete flexibility is found in all pages of the wizard, giving PCB designers as much control as they would like over the translation settings before committing to the actual translation process.
PCB DESIGN IMPORT PROCESS GUIDE
One type of Printed Circuit Board design project that’s frequently imported over is PCAD designs and projects. Since it’s a legacy software that’s no longer supported, users who own projects from PCAD, or receive PCAD files from a customer, would have difficulties even being able to open the files, let alone try to replicate them using a more current software platform such as Altium Designer. So what do you do?
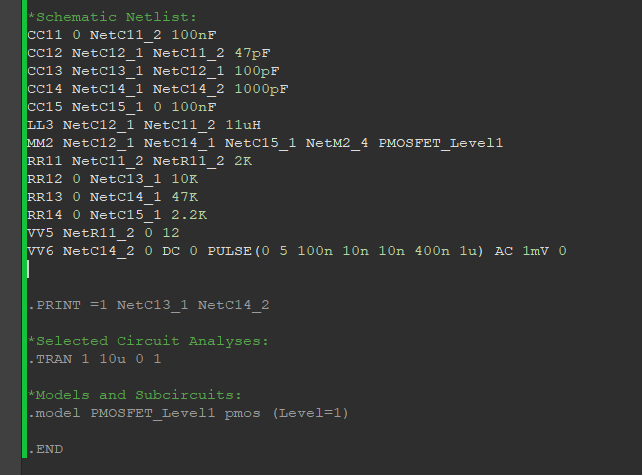
The following import steps and procedures are based on a particular design in PCAD, and show proof of concept for how the design can be translated into Altium. Similar concepts, edits, modifications and optimizations can be reused for other similar style designs as well as other design tool imports.

Figure 2 - Translate P-CAD Designs and Libraries
Once in the import wizard, a designer can then select the specific entry to be imported--in this case, the P-CAD Design and Libraries Files.

Figure 3 - Translate P-CAD Designs and Libraries
From there, you can add the specific Schematic Capture (. Sch) or PCB file (. PCB) files into the importer, where it would then analyze the files for processing. After that, you can match the layer of the specific design tool (PCAD) with a layer from the Altium Designer environment. Once these parameters have been set, the software will then allow you to select the directory and confirm output files.

Figure 4 - Output PCB Projects
With just a few simple actions, a user can easily transfer a design from PCAD over to Altium Designer. And PCAD is just one example. The Import Wizard functions the same way for any other supported importer design tool.

Figure 5 - Import Wizard Projects
CIRCUIT BOARD DESIGN VERIFICATION
Since you are importing a design from one application to another, depending on the input design, there may be some cases where manual cleanups and modifications are needed. There is no direct automated way to perform an Apple to Apple comparison. In this case, since you are not working with two different applications, the design data format, output generation will be different.
As part of the validity of the imported design into Altium Designer, it’s important to run through several Verification Criteria, in order to ensure the imported design is clean and the schematics are synchronized to the Printed Circuit Board. The most important tools available to users when transferring a design from one tool to another would be the Altium Designer Engineering Change Order (ECO) and Project Component Links.
There are two ways in which Altium Designer assists in the post process verification: Engineering Change Order and Component Links. The Engineering Change Order is a dialog box that shows the lists of modifications that can be made from one design (e.g. the schematic) to another design (e.g. the Printed Circuit Board). These design changes are required to satisfy certain modification needs in order to meet synchronization. This allows the designer, after the import, to synchronize the Circuit Board document with the source Schematic, or update component parameters directly from the libraries.

Figure 6 - Dialog Box Engineering Change Order
Another method Altium Designer uses, which assists users in verifying the consistency of the design post-import, would be the Component Links. This dialog enables users to check and control the status of the links between schematic component symbols and their corresponding PCB layout component footprints. Through this method, a user can match the components from one document to another through a variety of filters, such as by designator. A user can also match links between two document imports manually, thus allowing for versatility when importing documents from a different project file.

Figure 7 - Edit Component Links Dialog Box
As previously mentioned, since the import is coming from one design tool to another, 100% translation of the design project is impossible, due to basic differences in the two interfaces. Because of this, it is recommended that users perform a manual clean up on the Printed Circuit Board file.
Here are some of the proposed verification criteria:
- Compile Projects into Altium Designer
- Go through reported Warnings and Errors
- Resolve Warnings/Errors related to Schematic design
- Run Component Links to auto-match components between Schematics and Circuit Board
- Synchronize PCB Editor to Schematic Design via Engineering Change Order (ECO)
- Resolve Warnings/Errors related to PCB design
- Run Design Rules Check (DRC)
- Update Design Rules Constraints and resolve any DRC failure
- Generate documentation and output files
- Ultimately, a thorough Visual check of the Schematic and PCB
CONCLUSION
The Electronic Design Automation (EDA) software industry has led to a myriad of new Printed Circuit Board design software packages, which often function very differently from one another. The more PCB Design tools there are available, the more likely it becomes that a designer will have to convert a schematic capture from one tool to another, for a variety of different reasons. Many PCB designers may start a project on a free Printed Circuit Board design program like Kicad PCB or Designspark PCB only to find they require more advanced tools. The Altium PCB Design Import Wizard provides a quick and easy way to import designs from other tools into Altium Designer, making the two compatible and eliminating errors and discrepancies. By verifying the imported version consistency with the original project, the Altium Designer PCB design import wizard offers the highest level of accuracy, saving time and money.
 Open as PDF
Open as PDF