How Is Your Design Data Protected in Altium 365 GovCloud?

Altium 365 GovCloud is a dedicated region of the Altium 365 cloud platform, situated within the US and operated exclusively by US Persons in the AWS GovCloud region. This specialized environment is designed to help you meet the confines of US government regulations, providing a secure workspace for your team’s electronics designs. Read on for a deeper insight into how Altium 365 GovCloud protects your sensitive information to remain safe and accessible only to those who need it.
Encryption
Altium 365 utilizes the latest encryption technologies to ensure your design data remains secure, whether at rest or in transit.
For data at rest, once it’s hosted on the Altium 365 environment, it's processed through AWS. We employ AWS-provided key management and encryption modules meeting FIPS 140-2 requirements.
For data in transit, moving between customer environments and Altium 365, we rely on Transport Layer Security (TLS 1.2 or higher), the most widely accepted security protocol.
All connections within AWS use secure channels, enhancing the overall security of Altium 365. By actively phasing out outdated or vulnerable systems, we align with the standards recommended within the industry. Our encryption practices meet the rigorous requirements of FIPS for data at rest and NIST for data in transit.
Access Restrictions
The focus on security in Altium 365 GovCloud encompasses the entire platform, from the Web Application Firewall (WAF), allowing access only from US-based IP addresses, to the strict controls our DevOps team enforces.
The DevOps team is the only group granted access to the infrastructure and adheres to stringent access protocols to protect every node and piece of data. Their access is tightly controlled and subject to a thorough two-person approval process, which requires consent from both the team requesting access and our security team to ensure authorization is properly vetted and granted. We verify that every employee working within the Altium 365 GovCloud environment is a US person, as defined by federal regulations—this includes US citizens and green card holders. Every access request is backed by a thorough background check, a fundamental part of our hiring process.
When it comes to workspace access, Altium sets the initial controls, but then it's up to the workspace administrators to decide who gets in. Altium 365 GovCloud strictly blocks any IP addresses that are not US-registered or do not originate from a US location. However, your data's privacy and regulation are your responsibility in the sense of a shared responsibility model. Altium focuses on managing and protecting the infrastructure so that you don’t have to worry about technical issues such as updates to machines or databases.
Altium 365 GovCloud Status Page
Altium 365 GovCloud features a publicly accessible service status page, which relates to the availability of the platform. The page offers real-time updates, service statuses, incident disclosures, and more, ensuring that US customers have a reliable source of information to refer to at all times.

Incident Management
Altium boasts a comprehensive incident management program that thoroughly investigates incidents from multiple sources. Critical and high-severity incidents immediately activate the program, triggering a swift response covering everything from investigation to remediation.
Should these incidents affect our capacity to deliver services, we immediately report them on the Altium 365 GovCloud Status Page.
Vulnerability and Threat Management (VTM)
To minimize the probability of incidents, Altium has implemented a vulnerability and threat management program. This program is designed to identify vulnerabilities early in the code development phase, even before it’s deployed in production, as part of our secure software development lifecycle. We utilize advanced protections like Software Composition Analysis (SCA) to identify vulnerabilities not only in our existing code but also in any third-party libraries that are being integrated.
Additionally, the code is being monitored continuously. In the live environment, our threat detection tools are always active, collecting threat intelligence from various data sources. We constantly monitor the environment for any emerging threats and respond accordingly.
This meticulous approach is consistent across both Altium 365 GovCloud and our commercial offerings, though, with GovCloud, we adopt additional efforts to ensure compliance with regulatory requirements.
Network Security
Now, let’s look at Altium 365 GovCloud controls that help manage both unauthorized inbound and outbound traffic.
As mentioned, Altium 365 GovCloud implements firewall restrictions to block IP addresses from outside the US. This includes the use of a Web Application Firewall (WAF) that restricts inbound access.
For outbound access, Altium 365 GovCloud employs controls that allow you, the customer, to set your own restrictions on IP addresses as well. We don’t monitor whom you grant access to. It is the responsibility of the customer to determine who has access, the level of access granted, and whether they have the capability to download and export data.
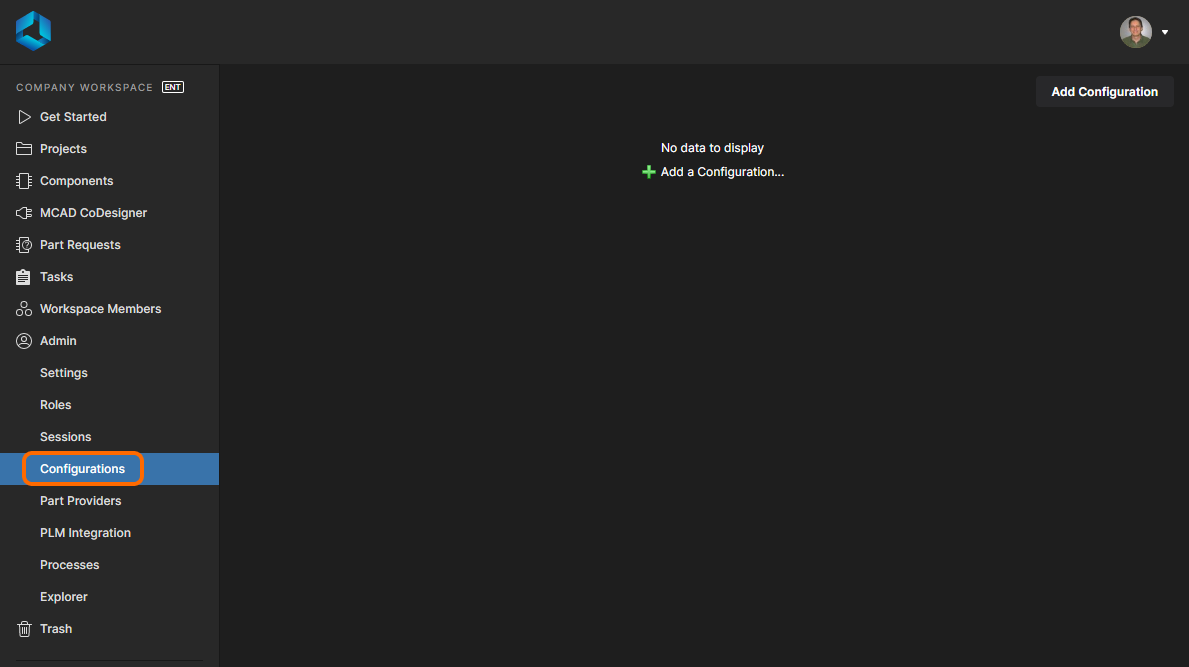
Only the admin has the authority to add or remove users from the workspace. The admin is designated as either the owner of the workspace or an appointed administrator. The owner of the workspace is automatically an admin, and other users can be granted admin status as well.
As an admin, you can see who has access, and you have the authority to revoke access as needed. Only admins can perform critical workspace operations, ensuring that sensitive actions are tightly controlled and managed.
Since admins have the ability to add an email address for anyone they wish to grant access to the environment, it's crucial to carefully control who is given this power.
In an Advanced Security Package, we also include IP Whitelisting, which is an exclusive privilege of the admin. It's not possible for just anyone to add themselves or their IP addresses to the whitelist.
Get Your Copy of the Security Whitepaper
Through meticulous encryption, stringent access restrictions, and strong network security, we ensure that your electronics design data is not only secure in Altium 365 GovCloud but also managed within a framework that respects and upholds the highest standards of data protection. Our commitment to safeguarding your projects extends from the ground up, incorporating a comprehensive security strategy that covers every aspect of our platform's operation.
Discover more about the security approach, measures, and practices of Altium 365. Get your copy of the security whitepaper to gain the insights you need, or visit our Trust Center.