IoT Security: Physical Layer Security for IoT PCBs
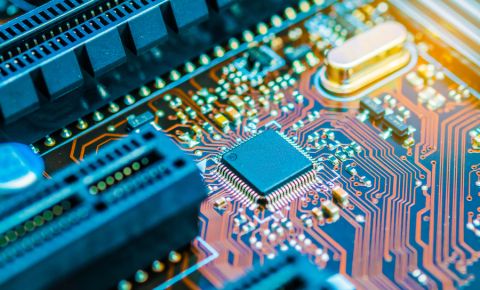
Internet of Things security will be a big issue as the IoT expands.
Have you ever had your house broken into? I haven’t, but the door was kicked in on the other side of our duplex once. It was scary to realize that a thief could break into my house with nothing more than their legs. After that, we reinforced our door frame and added an extra deadbolt to make it harder for someone to rob us. It may surprise you to find out that the Internet of Things (IoT) devices you design are also susceptible to break-ins.
IoT items are often left out in the open and are physically insecure. With the right physical tools, an attacker can easily break into a device. They can then either hack it or read sensitive data from it.
EMI Shielding
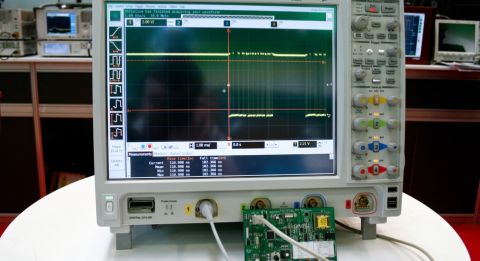
While you may normally think about EMI in terms of interference and the FCC, EMI is also a very important aspect of security. Radiated EMI can give attackers information on what’s going on in your . Injected EMI can let hackers manipulate or confuse your circuits. The answer to both problems can be shielding.
Only electromagnetics nerds, like myself, are really interested in totally reducing EMI during PCB design. Most designers just use the normal mitigation strategies and hope that their circuit board passes certification. Well, you might want to try harder and curtail all crosstalk in your circuits. Passive EMI coming out of your circuit board can give attackers an idea of what’s going on inside your circuits. Low-cost EMI sniffing tools are now readily available. Shielding your circuit will ensure that no signals are left out in the open.
Self-radiated EMI isn’t the only thing you have to worry about. As you know, AC systems are often susceptible to EMI. Attackers can use this to their advantage by injecting signals into your AC systems via EMI. A shield can be a great way to try and ensure that no malicious signals find their way into your circuit. Now, shielding won’t guarantee your PCB’s safety. If a person is able to take apart your circuit board enclosure, they may be able to physically remove any shielding. At that point, reducing EMI won’t help you, you’ll have to move on to other physical steps.
You could become an electronic detective.
Tamper-Proof Circuits
IoT applications and devices are often sitting in the open, in their owned pocket, or even on a dinner plate. That makes it hard to be sure some nefarious person won’t get their hands on the PCB inside. The best way to mitigate this risk is with tamper proof boards.
You’re probably not responsible for designing the impossibly small enclosures for your boards. So you can’t design them to be physically secure. Your job is to detect if someone has gained access to the printed circuit board. If you know the board has been compromised, you can enact countermeasures. There are several different ways to detect tampering. You could use physical switches that are triggered when the device is opened. You could also seal your board in some kind of wrapper that detects when it is breached.
Once an intrusion has been detected you could react with a variety of physical countermeasures. You might cut the power to the connected device, though this is not guaranteed to wipe the memory. If you only need to know about tampering, the device could simply log the intrusion. On the extreme end, you could physically destroy your device with a small explosive. I wouldn’t recommend that approach for the majority of IoT products. While tamper-proofing your PCB is a great idea, it can be expensive, so keep an eye on your budget.
Cutting the shape of a lock into your board will not make it more secure.
Masking Electronic Components
So let’s say that someone has gained access to your PCB. Your boss didn’t approve any of those expensive countermeasures, so you’re pretty much screwed. Not so fast, there are a few other inexpensive, board level, security measures you can employ.
Once they have invaded your enclosure, hackers often like to read passive information from your circuits. Things like power usage, I/O pins, and test points can help villains decrypt secured information or attack your board. There are a few ways you can protect your circuits from these probes.
-
Cover chips in epoxy - It may not seem like an elegant solution, but it can be effective. If your pins and electronic components are painted in epoxy it will be more difficult for attackers to access them.
-
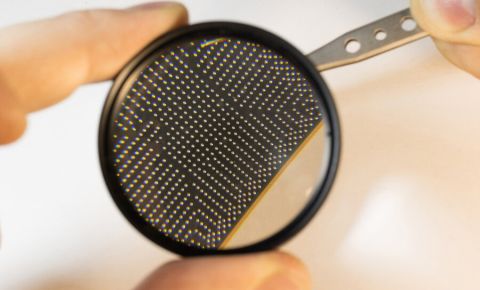
Use difficult to access components - Some components are naturally hard to tap into. Ball grid arrays (BGAs), for example, have all contacts underneath the package. This makes it a tricky job to spy on pins.
-
Use buried vias - Buried vias will not only save space, they’ll also protect information. It’s nearly impossible to probe a buried via. Whatever is being transmitted on it is effectively safe.
-
Nonconductive via fill - Filling, tenting, or plugging vias with a nonconductive compound will help ensure the via won’t be easily probed.
-
“Black out” chips - If an attacker knows what chip they’re looking at, they can expose its known vulnerabilities. Defacing your chips so that their identity is unknown will give hackers a harder time.
None of these strategies are guaranteed to keep your IoT device totally secure. If someone is determined enough, they can probably hack into your PCB. The best you can do is try and mitigate as much risk as possible. Reducing EMI, making your PCB tamper resistant, and masking components and traces on your board will lower your security risk.
Some of the things I’ve suggested here are simple, like shielding. Using lots of buried vias and tamper-proofing your PCB can be a tad bit more complicated. Some good PCB design software will help you employ the techniques laid out in this article. CircuitStudio® has a wide variety of features that can help you design the most secure board you are able to.
Have more security questions? Call an expert at Altium.